The Mythos and the Quantum moments (Part 2/2)
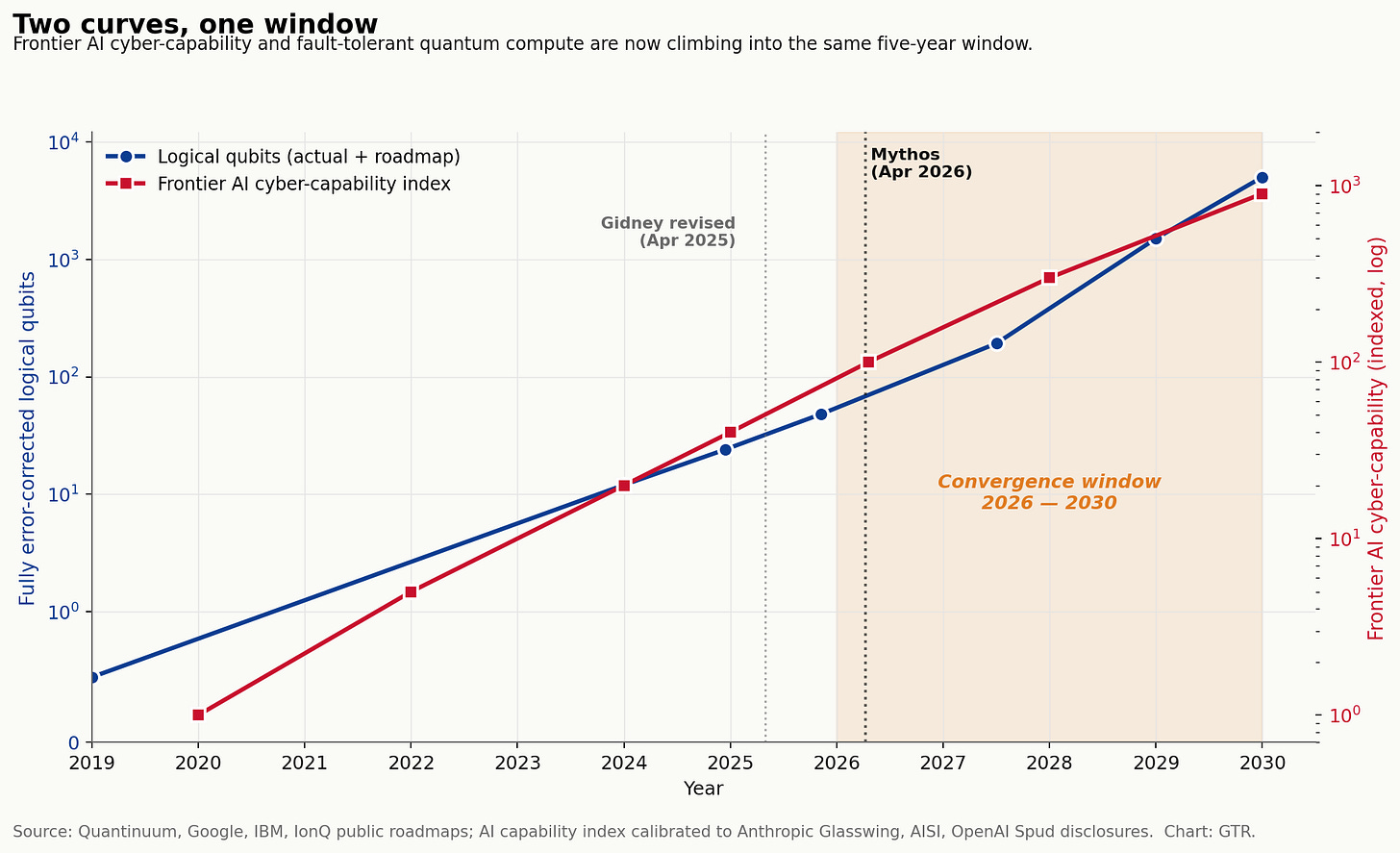
Part 2 of 2 — Mythos broke code. Quantum will break the math underneath it. Two revolutions, one widening asymmetry, and the eighteen months the C-suite should not waste
In Part 1, the argument was simple and uncomfortable: every generation of cyberattack has made the offence cheaper, faster, and more concentrated, and Anthropic’s Claude Mythos Preview — gated behind twelve corporate partners — was the sharpest expression of that pattern yet. A 27-year-old vulnerability in OpenBSD, a 16-year-old flaw in FFmpeg, a Linux kernel privilege escalation chained in a weekend. The defenders pay retail. The attackers pay wholesale.
Mythos breaks code.
Quantum, when it arrives, will break the math the code is sitting on. And the strangest part of the next eighteen months is that those two timelines, which most boards still treat as separate problems, are starting to collapse into one.
A short history of breaking math
Before the cryostats and the satellites, there was a lecture room in Santa Fe.
November 1994. Santa Fe, New Mexico. Peter Shor, a thirty-four-year-old combinatorialist at AT&T Bell Labs, walks to the front of the 35th Annual Symposium on Foundations of Computer Science and presents a paper titled, in the dry register of the field, Algorithms for quantum computation: discrete logarithms and factoring. The result has already leaked. Months earlier, Shor gave an informal talk in Henry Landau’s Tuesday seminar at Bell Labs on the discrete-log piece. By the weekend he was at home with a cold when Umesh Vazirani called from Berkeley. I heard you know how to factor on a quantum computer, Vazirani said, per Shor’s reconstruction for Physics Today thirty years later. Tell me about it. Shor had not yet figured that out. Well, he answered, this is a game of telephone. He spent the weekend doing it. The factoring algorithm — the one that, given a sufficiently large fault-tolerant quantum computer, will break essentially every public-key system on the internet — was finished in a sickbed before its author had told most of his colleagues it existed. John Preskill, hearing about it, called it an eye-opener. It made me feel that this was a serious business. The cryptography community understood immediately. There was now a known-broken date on RSA. Nobody knew when it would arrive.
September 29, 2017. Vienna and Beijing, simultaneously. A 75-minute video call connects Anton Zeilinger at the Austrian Academy of Sciences to Chunli Bai at the Chinese Academy in Beijing. The call is unremarkable except that the encryption keys protecting it are not protected by math. They are protected by physics. Above them, at roughly five hundred kilometres’ altitude and 18,000 miles per hour, the Micius satellite — named after the fifth-century BCE Chinese philosopher Mozi — passes over Graz, beams a stream of polarised photons down to a ground station, then passes over Xinglong near Beijing and beams a second stream. Onboard, Micius XORs the two keys and broadcasts the result. Anyone trying to listen in would have to measure the photons in flight, and measurement disturbs the polarisation, and the disturbance shows up immediately in the receivers’ error rate. To demonstrate the link, Pan Jianwei’s team exchanges two images, each about five kilobytes. From Beijing, a portrait of Micius the philosopher. From Vienna, a portrait of Erwin Schrödinger. Two philosophers of knowledge, one ancient, one modern, crossing 7,600 kilometres of vacuum at the speed of light, pixels secured by quantum uncertainty. This is a very important step towards a world-wide and secure quantum internet, Zeilinger says. The peer-reviewed paper appears four months later in Physical Review Letters. The relevant point is the geography. The first intercontinental QKD link was not Boston-to-London. It was Beijing-to-Vienna.
October 23, 2019. Santa Barbara, California. A leak forces the announcement five weeks early. On September 20 the Financial Times finds a Google paper accidentally posted on a NASA server and pulls it down before it disappears. By October 21, IBM has already published a rebuttal. On the 23rd, Nature publishes the actual paper — a 53-qubit superconducting chip called Sycamore, sampling random circuits in 200 seconds where Google estimates a classical supercomputer would need 10,000 years. IBM says 2.5 days, with enough disk and a clever algorithm. John Martinis, the experimental lead, says the paper is mostly relief that everything worked. Sundar Pichai compares the chip to the Wright brothers’ twelve-second flight. Brooks Foxen, a Martinis Group graduate student, puts the gap more crudely: we are currently 1.5 trillion times faster. The thing the world had to absorb was not the 10,000-year claim. It was that the curve had inflected. Quantum hardware was now, in at least one narrow benchmark, beyond classical reach.
December 9, 2024. Santa Barbara again. Five years after Sycamore, Hartmut Neven posts a blog announcing Willow, a 105-qubit chip. The headline number is 10 septillion years versus under five minutes — the new random-circuit-sampling result. The number that matters is buried lower. For the first time, Google demonstrates quantum error correction below threshold: as the surface code grows from 3×3 to 5×5 to 7×7, the logical error rate falls instead of rising. The suppression factor is Λ = 2.14 ± 0.02 per increase of two in code distance. The logical qubit lives 2.4 times as long as the best physical qubit underneath it. Sundar Pichai posts about it on X. Elon Musk replies, Wow. The internet spends two days arguing about parallel universes. Scott Aaronson spends much of December 10 gently correcting that interpretation while confirming the milestone is real. After 30 years, he writes, we’re now finally tickling the tail of the dragon of quantum fault-tolerance, the dragon that — once fully awoken — will let logical qubits be preserved and acted on for basically arbitrary amounts of time, allowing scalable quantum computation. The dragon is not awake. It has begun to stir.
Those are the four scenes. The thirty-year arc from a sickbed in New Jersey, to a satellite over Eurasia, to a 53-qubit chip in California, to the moment the error-correction math finally started working, is the prehistory of the quantum security revolution. The revolution itself starts now.
Where we actually are
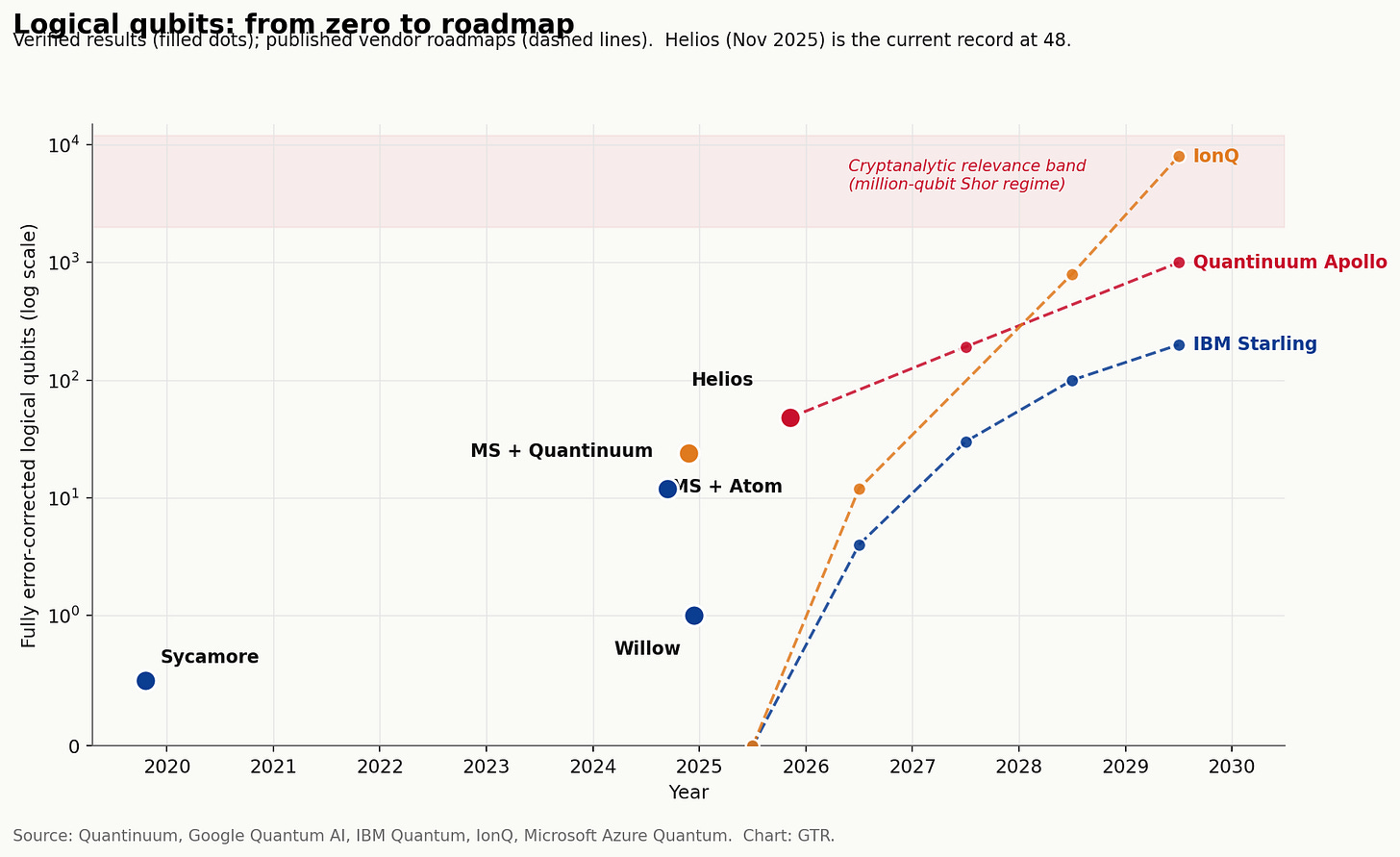
It is tempting to read the Willow blog post and conclude that fault-tolerant quantum computing is here. It is not. The most honest snapshot of the field as of May 2026 is this: the highest verified count of fully error-corrected logical qubits in any operating system is 48, demonstrated by Quantinuum’s Helios ion-trap machine in November 2025, on 98 physical qubits at a 2:1 encoding ratio. Helios’s two-qubit gate fidelity is 99.921 percent across all qubit pairs. Its single-qubit fidelity is 99.9975 percent. Those are the highest numbers any commercial system has ever published. Forty-eight logical qubits is also a long way from breaking RSA-2048.
The interesting thing is the slope, not the level.
In 2019, Sycamore had 53 physical qubits and zero logical qubits. In December 2024, Willow had 105 physical qubits and the first credible demonstration that error correction can scale. In November 2025, Helios pushed the logical-qubit number into the dozens with magic-state production at an infidelity of 7×10⁻⁵, what the field calls a fully fault-tolerant universal gate set. IBM’s public roadmap, updated in June 2025, targets a system called Starling for 2029: 200 logical qubits, 100 million gates, built at IBM’s Poughkeepsie campus. The intermediate steps are named — Loon in 2025, Kookaburra in 2026, Cockatoo in 2027 — and each one is a specific architectural bet on quantum LDPC codes that reduce the physical-qubit overhead for error correction by roughly ninety percent versus surface codes. Quantinuum’s accelerated roadmap targets Apollo — thousands of qubits, fully fault-tolerant — for 2029. IonQ targets 80,000 logical qubits by 2030. PsiQuantum, which raised a $1 billion Series E in September 2025, is building photonic million-qubit facilities in Brisbane and Chicago and has not yet operated a public machine. Microsoft, in February 2025, unveiled Majorana 1, eight topological qubits on a chip designed to scale to a million. Atom Computing’s AC1000, also from 2025, is a 1,200-physical-qubit neutral-atom array.
Five technologies. Five roadmaps. All converging on the same five-year window.
In April 2026 IBM’s CEO Arvind Krishna told Reuters the company expects “early examples of quantum advantage this year.” More striking: in March 2026, Google’s own security team announced that Google had set a 2029 internal target for migrating its production systems off classical public-key cryptography. The reason given was straightforward. The factoring estimates have collapsed.
The factoring estimates have collapsed
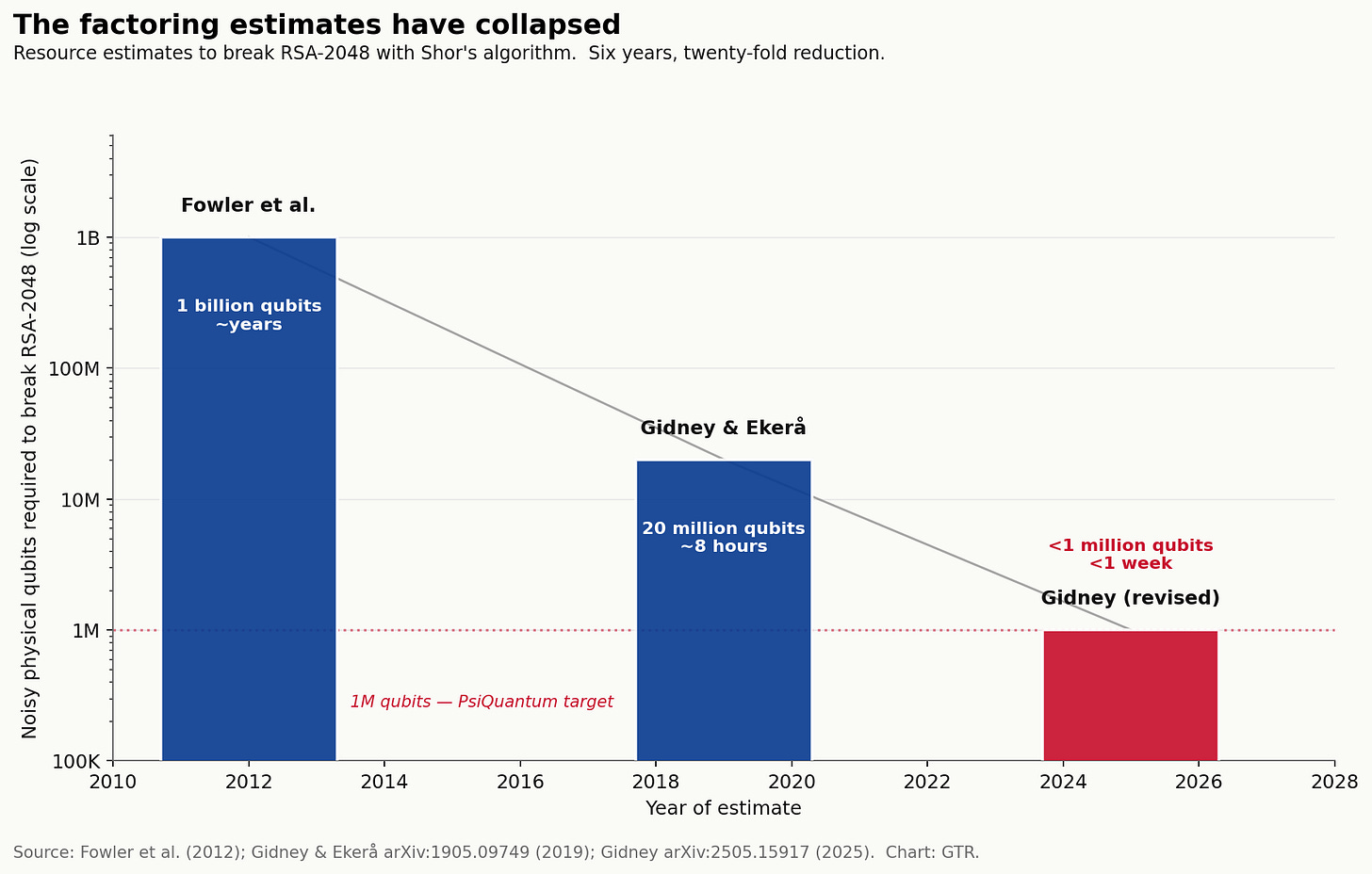
In 2012, Austin Fowler and colleagues estimated that breaking RSA-2048 with Shor’s algorithm would require roughly one billion noisy physical qubits.
In 2019, Craig Gidney and Martin Ekerå tightened that to 20 million qubits and eight hours.
In April 2025, Gidney published a revision — under one million noisy qubits, under a week. Roughly a twenty-fold reduction in six years.
The trajectory is what matters. The crypto-apocalypse was once thought to be a billion-qubit problem on a thousand-year horizon. It is now widely modelled as a million-qubit problem on a five-to-ten-year horizon. The Mosca survey of cryptographic experts run by evolutionQ put the probability of a cryptographically relevant quantum computer within ten years at 49 percent in 2025 — the highest reading the survey has ever recorded, up from 34 percent the year before.
Forty-eight logical qubits today. Two hundred logical qubits targeted for 2029. The gap to the cryptanalytic threshold is closing in a recognisable way. Boards that internalised “quantum is decades away” are working from a model the technical community no longer holds.
Harvest now, decrypt later
The reason this matters today, not in 2030, is harvest-now-decrypt-later. An adversary that records encrypted traffic now and stores it cheaply has a free option on every future quantum machine. Anything still under classical encryption when fault tolerance arrives — diplomatic cables, source code, biometric records, design files, financial settlements, intelligence intercepts, twenty-year mortgages with private-key authentication — is decrypted retroactively.
This is not a theoretical posture.
The NSA flagged it in August 2021. The Five Eyes joint advisory AA23-144A named Volt Typhoon, the Chinese state-affiliated cluster targeting US critical infrastructure. The Salt Typhoon campaign, disclosed across 2024 and 2025, compromised at least nine US telecoms and roughly 100,000 routers; the FBI has called it the most significant cyber-espionage campaign in US history. What was sitting on those routers? Years of call metadata, signalling, lawful-intercept routes, and the encrypted traffic that flowed through them. Some of that traffic is being held. A January 2026 Federal Reserve working paper walked through the systemic risk of historical financial transcripts becoming decryptable. ANSSI, France’s cybersecurity authority, has effectively assumed HNDL in its hybrid PQC requirements. Germany’s BSI has set 2031 as the deadline for hybrid PQC across regulated systems and 2030 for classified ones.
If you operate a system whose data has a confidentiality lifetime longer than five years, the practical assumption is that hostile capture is happening now. Q-Day is not the day quantum computers break RSA. Q-Day is the day everything captured up to that point is decrypted.
The migration is already underway, and it is unevenly distributed
NIST, after an eight-year process, finalised the first three post-quantum standards on August 13, 2024. FIPS 203 (ML-KEM, formerly Kyber) for key establishment. FIPS 204 (ML-DSA, formerly Dilithium) for signatures. FIPS 205 (SLH-DSA, formerly SPHINCS+) as a hash-based backup. FIPS 206 (FN-DSA, the Falcon variant) is in draft. HQC, a code-based backup KEM, was added in March 2025.
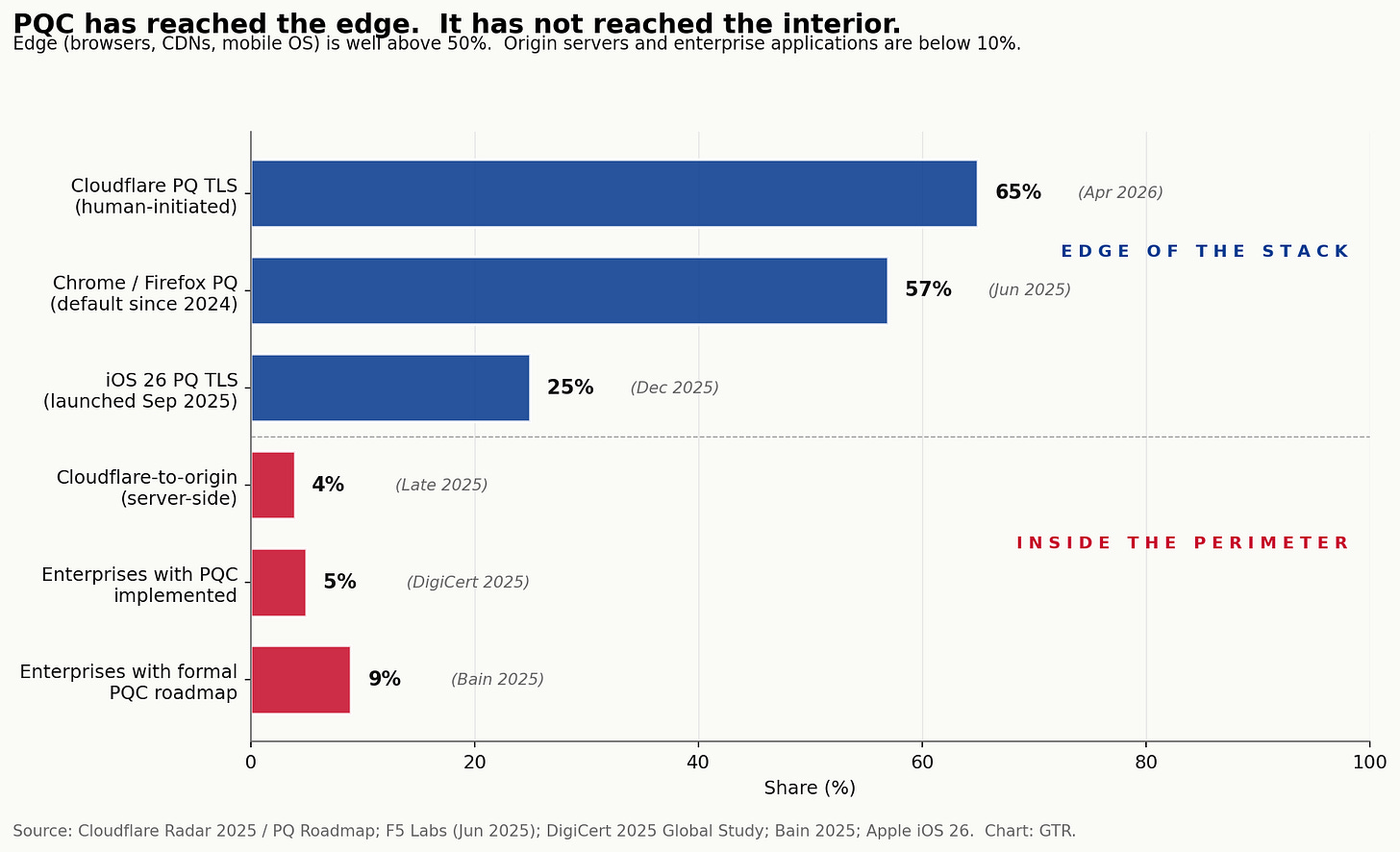
The standards were the starting gun. The deployment has been faster and more lopsided than most boards realise.
Cloudflare measured 52 percent of human-initiated TLS 1.3 traffic across its network as post-quantum-encrypted by December 2025, rising above 65 percent by April 2026. Apple shipped iMessage PQ3 in February 2024 with hybrid Kyber-1024 key establishment and rekeying every fifty messages or seven days. iOS 26 added PQ TLS in September 2025; within four days, the share of iOS device requests using PQ encryption jumped from under two percent to eleven percent on Cloudflare’s measurements. Signal rolled out PQXDH in September 2023. Chrome enabled hybrid PQ key agreement by default on Desktop in March 2024 and on Android in November of the same year. AWS KMS added ML-DSA signatures in June 2025; Amazon S3 added ML-KEM TLS in November 2025. Microsoft made PQC APIs generally available on Windows Server 2025 and Windows 11 in November 2025. OpenSSH 10.0, in April 2025, defaulted to ML-KEM hybrid key exchange. OpenSSH 10.1 prints a warning to users when a non-PQ exchange is negotiated: this session may be vulnerable to store-now-decrypt-later attacks.
That is the upper layer of the stack. The lower layer tells a different story. Cloudflare’s own data shows that origin-server PQ readiness — the connection from Cloudflare to the actual application — sat at 3.7 percent in late 2025. The DigiCert 2025 global study found that 69 percent of enterprises acknowledge quantum computers will break current encryption by 2030 and only five percent have implemented quantum-safe encryption. A Ponemon study for Entrust put the number of organisations with no formal PQC roadmap at well over half. The Bain survey put it more bluntly: 71 percent of executives expect a quantum-related cyber event within five years; nine percent have a plan.
The defenders are paying retail again.
The convergence
This is where Mythos comes back into the room.
For three decades the security community modelled the LLM threat and the quantum threat as separate. One was about software bugs in code humans wrote. The other was about mathematical primitives the code was sitting on. The mitigation timelines were different. The vendors were different. The board committees responsible were, in most large organisations, different.
That separation no longer holds. Three convergence vectors have to be priced into any 2026–2030 plan.
The first vector is co-design. Mythos-class models are now being used to optimise quantum error-correction decoders in real time, to discover surface-code variants better than the ones humans wrote, and to do the high-dimensional simulation needed to verify quantum results. IBM’s relay-BP decoder, Google’s real-time decoders running at 63 µs latency on Willow, Quantinuum’s magic-state distillation circuits — all of them rely on machine-learning techniques whose pace has accelerated since Mythos shipped. The same partner ecosystems that gate Mythos — AWS, Google, Microsoft, IBM — gate the leading quantum stacks. The two technology trees share roots.
The second vector is implementation attacks. A cryptographic primitive can be mathematically secure and still leaked through its implementation. Side-channel attacks, fault-injection attacks, timing attacks, padding-oracle attacks — these are software bugs in cryptographic libraries, and Mythos is, exactly, a finder of software bugs. ML-KEM and ML-DSA are new code, deployed in haste, in libraries written under deadline pressure across thousands of vendors. The first wave of PQC libraries is already accumulating CVEs. A Mythos-class model, pointed at a freshly written ML-KEM implementation, finds bugs in the implementation faster than the implementation finds bugs in itself. The defender’s window-of-vulnerability between standard and hardened deployment is exactly where attackers earn outsized returns.
The third vector is timeline collapse. The classical assumption was that the LLM threat would land in 2025–2027 and the quantum threat in 2032–2035, giving organisations a clean handoff. Mythos arrived in April 2026. Gidney’s revised factoring estimate landed a year earlier than expected. NIST’s standards published a year earlier than the original 2025 target. Cloudflare moved its full-PQ-suite roadmap from 2030 to 2029 in April 2026. Google moved its internal migration target to 2029. The two threats are not arriving in sequence. They are arriving in the same five-year window, into the same boardrooms, often through the same vendor relationships.
The asymmetry from Part 1 reasserts itself. The offence is concentrated. The defence is fragmented. The defenders are reading two roadmaps, three NIST standards, two AI-safety frameworks, and twelve vendor pricing pages. The attackers are reading one playbook: capture now, exploit later.
The Glasswing parallel
Quantum has its own version of Project Glasswing.
IBM’s Quantum Network has more than 300 members, but the meaningful access — to current Heron and Nighthawk hardware, to the fault-tolerance roadmap, to the Starling preview programme — sits inside a much smaller ring of strategic partners. AWS Braket gates IonQ, IQM, QuEra, Rigetti, and AQT through a single billing relationship. Azure Quantum gates Quantinuum, IonQ, and Atom Computing. Google Quantum AI’s industrial partners are not enumerated publicly. DARPA’s Quantum Benchmarking Initiative selected eleven companies for Stage B and gave Microsoft and PsiQuantum a separate Phase 3 track. The export controls on dilution refrigerators, on cryogenic control electronics, on photonic-foundry capacity, and on certain trapped-ion components are tightening every quarter. China’s CN-QCN already runs over 12,000 kilometres of fibre, with 145 backbone nodes and Jinan-1 satellite extension; the 15th Five-Year Plan has named quantum the first of seven future industries, with reported total investment up to $17.6 billion. The EU’s EuroQCI network covers all 26 participating member states with a planned satellite, Eagle-1, late in 2026 and a fully operational network by 2030. The UAE and Qatar have committed roughly $1.6 billion combined; Saudi Aramco signed with Pasqal for a 200-qubit system.
The pattern is identical to Mythos. Concentrated capability, gated access, sovereign blocs, partner perimeters. The non-partner — the mid-cap utility, the African telco, the Latin American bank — gets the standards, eventually, and the cryptographic refresh, eventually. By that point, the partners have been running on hybrid PQ stacks for four years.
The same trade applies. The partner perimeter is structurally long. Outside the perimeter is structurally exposed.
What it means for the C-suite
Three things follow for any board reading this in May 2026.
First, treat post-quantum migration as an operational programme, not a research line. The migration is not waiting for fault-tolerant quantum to arrive. It is being driven now by regulatory deadlines (CNSA 2.0’s 2027 acquisition cutoff for US national-security systems, NCSC’s 2031 milestone, BSI’s 2031 hybrid mandate, the EU’s coordinated 2030 push), by infrastructure providers shipping PQ defaults, and by the harvest-now reality that anything captured today will be readable when the math breaks. The first deliverable is a cryptographic inventory across TLS, VPN, KMS, signing certificates, code-signing pipelines, firmware update channels, hardware roots of trust, and third-party APIs. Most large enterprises do not have one. The Campbell migration estimates put a typical large bank’s full crypto rollover at twelve to fifteen years. Starting in 2026 places the finish line at 2038–2041, well after a plausible Q-Day. There is no scenario in which the unprepared organisation finishes on time.
Second, the AI-cyber and quantum-cyber programmes belong on the same agenda. If a CISO is reporting to one committee on Mythos exposure and to a different committee on PQC readiness, the convergence has not been internalised. The questions are the same. Which third-party vendors hold our cryptographic primitives? Which of those vendors is in a partner ecosystem that has access to frontier offensive capability — Mythos-class scanning, fault-tolerant simulation, classified threat intelligence? Which of those vendors will be slower to patch than the attacker is to find? The answer should not require two separate working groups.
Third, the geographic frame matters. For a regulator in Riyadh, Abu Dhabi, São Paulo, Lagos, or GIFT City, the question is not whether to follow NIST. It is whether to follow NIST alone, follow ANSSI’s mandatory hybridisation, follow BSI’s 2031 deadline, build a sovereign track aligned with China’s CN-QCN, or design a hybrid that covers all of them. The early movers — Singapore’s CSA Quantum-Safe Handbook in October 2025, the UAE’s national PQC programme, Saudi Aramco’s Pasqal partnership — are already acting on the assumption that cryptographic sovereignty is a national-security question, not a procurement question. The non-aligned, the late, and the under-resourced will inherit whichever regime their largest vendor decides to ship.
What it means for investors
Part 1 mapped the cybersecurity tape into Glasswing partners and non-partners. Quantum will not be that clean, and the most useful framing is not a list of tickers — most pure-play public quantum names trade on narrative, dilution, and a five-year revenue gap — but a set of structural exposures.
The picks-and-shovels layer is where the math is most defensible. Cryostats, dilution refrigerators, RF and microwave control electronics, cryogenic CMOS, photonic foundry capacity, specialty optics, single-photon detectors, ion-trap chips, and the laser systems that drive them. Every credible roadmap to 2029–2030 needs orders of magnitude more of all of this. The supply chain is concentrated, export-controlled in places, and the leading suppliers are already capacity-constrained.
The PQC-services layer is where the budget is most certain. Cryptographic inventory tooling, hardware-security-module refreshes, firmware-signing migrations, certificate-authority rebuilds, and the systems-integration spend behind every regulated industry’s 2030 deadline. The same handful of integrators that did the FedRAMP migration and the Y2K rollover will do this one, at higher margins.
The sovereign-quantum trade is the longest-duration. China is building its own stack at scale. The EU is funding EuroQCI with a 2030 operational target. The UAE and Saudi Arabia are buying access. India, Singapore, and Japan are formalising national programmes. The capital coming into sovereign quantum infrastructure over the next decade will be larger than the entire current public-quantum market cap. Most of it will not be visible in the listed equity tape until the contracts are signed, and most of those contracts will not be available to non-aligned investors. The trade is not a basket. It is a relationship.
The cyber-incumbent trade from Part 1 still applies, with one twist. The cybersecurity firms inside the Glasswing perimeter — the ones briefed on Mythos-class capability — are also the ones likeliest to land the PQ migration contracts inside their existing customer base. The cross-sell from Mythos defence to PQC migration is real, and it accrues to a small group of incumbents. Outside that perimeter, the trade is the same as Part 1: the unprepared get repriced.
We do not give specific tickers in a public letter. We give structure. The structure is: long the convergence, long the picks and shovels, long sovereign infrastructure where access exists, short the unprepared.
A modest provocation
The 2035 migration deadline that NSM-10 set, that NCSC echoed, that BSI quietly aligned to, that most enterprise PQC programmes have used to anchor their planning, is a fiction.
The deadline that matters is whichever year the attacker can decrypt 2025’s captured traffic. Nobody knows that year. The most credible expert survey says 49 percent probability inside ten years. Google has internalised 2029. Cloudflare has built its own roadmap to 2029. The Gidney revision, applied to a million-qubit photonic system in Brisbane or Chicago, is not absurdly distant. The Mythos arrival, eighteen months ahead of its central forecast, has shown what happens when capability outruns expectation.
Treat 2030, not 2035, as the planning horizon. Build to a hybrid that survives both. Assume the data captured this week is on a five-to-ten-year clock. Assume the partner perimeter widens, not narrows. Assume Mythos-class models will find every shortcut taken in the first wave of PQC code, the same week the code ships. Assume sovereign quantum stacks will fragment the global cryptographic regime into three or four blocs by 2030, each with its own approved primitives, its own audit regime, its own export controls.
Cybersecurity, for the last thirty years, has been a problem of patching software that humans wrote against attackers who got better with each generation. Mythos broke the symmetry on the software side. Quantum is breaking the symmetry on the math side. The two are not separate problems and they are not arriving on separate timelines. They are arriving together, into a defender base that has not yet built the muscle for either, and a partner club that is widening, not narrowing.
Plan for 2030.
What I’m watching
IBM Starling proof-of-concept in 2028, full system in 2029. The 200-logical-qubit milestone is the first one that gets within an order of magnitude of cryptanalytic relevance.
Quantinuum’s Apollo in 2029, and whether Helios’s two-qubit fidelity records hold as the system scales to thousands of qubits.
The first verified Shor-on-toy-RSA. Not RSA-2048, but a real factoring of a real semiprime at, say, RSA-300. The day that paper is published is the day every CIO in the regulated world rewrites their migration plan.
EuroQCI’s Eagle-1 satellite late this year and the operational network in 2030. The first sovereign QKD network at continental scale.
The first major non-partner PQC breach. A bank, a telco, a logistics network whose ML-KEM implementation is found to have an exploitable bug — by Mythos or by something downstream of it. That is the moment the convergence stops being theoretical for boards.
The 2027 acquisition cutoff under CNSA 2.0. Every government RFP from January 2027 that omits PQ requirements is informative — about which vendors are ready, which agencies are flexible, and which contracts will quietly slip.
— GTR Team